May 03, 2023
Discovering the Secrets of the Dark Web: A Guide to Accessing the Underworld

Monitoring the dark web is crucial for faster incident response and better protection against data breaches. As seen with the Marriott Starwood breach, it can take years before a company even realizes that their system has been compromised. With the dark web constantly evolving, it's important to stay ahead of the game and monitor for any potential threats. Without this monitoring, companies may not even be aware that a breach has occurred for months. By staying vigilant and regularly monitoring the dark web, businesses can better protect themselves and their customers from cyber threats.
Explore the Dark web report and access the latest findings. Discover the key features of monitoring the dark web, including threat intelligence, threat hunting, faster incident response, and integration into security platforms. To safeguard your organization against the dark web, there are some proactive measures you can undertake. These include conducting regular monitoring and surveillance of the dark web, implementing robust security protocols, and staying up-to-date with the latest security trends and technologies.
When it comes to monitoring the dark web, it's important to understand that not all areas can be scanned. The vastness of the dark web makes it impossible to scan every corner of it. Although search engines dedicated to the dark web exist, they pale in comparison to the scope of Google's search capabilities.
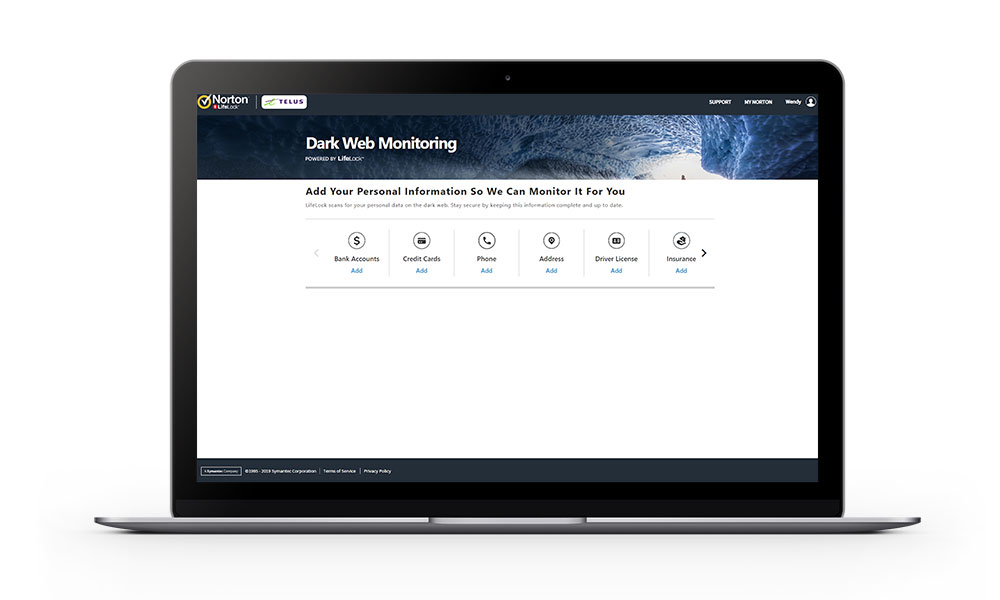
Ensuring added convenience, the monitoring of the dark web can now be done simply by unlocking your device. Google One is dedicated to protecting your information and respecting your privacy, thus keeping you safe online. Discover how Google One helps you stay in control while safeguarding your online activities.
Traversing the Mysterious Realm of the Dark Web - A Guide to Accessing It
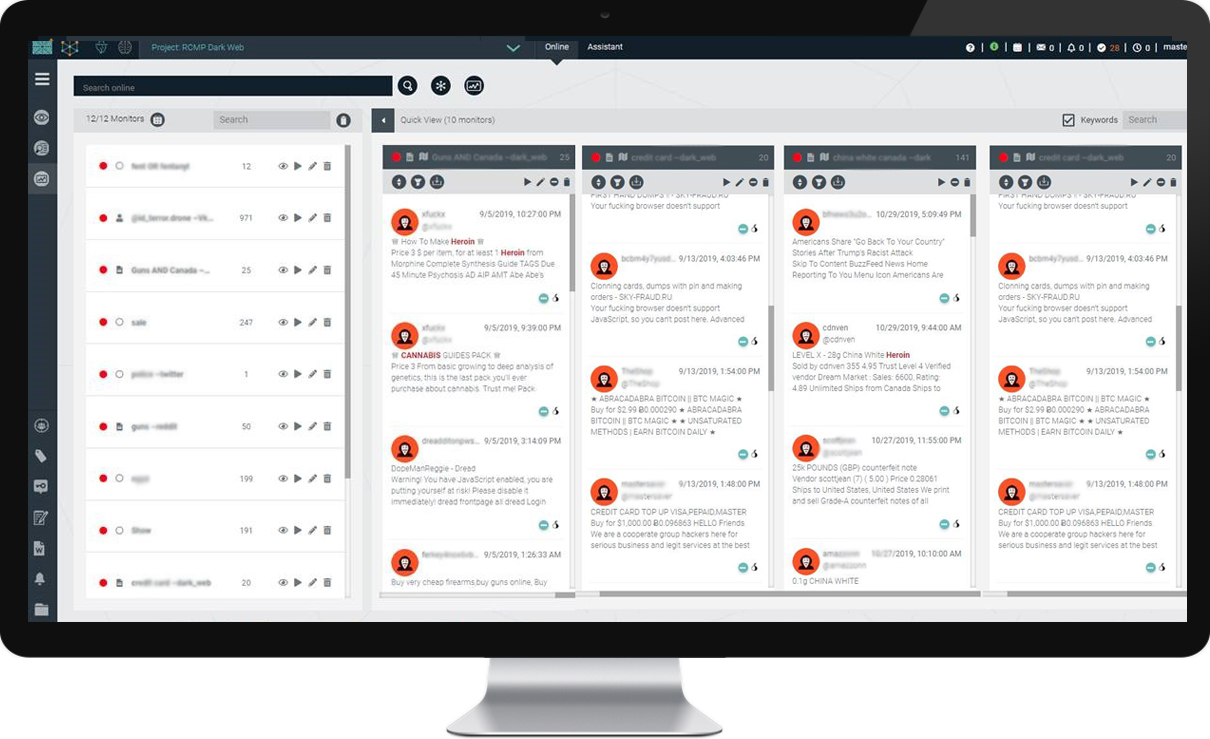
Monitoring the Dark Web: Ensuring Your Company's Information is Safe
When it comes to the dark web, it's important to stay vigilant. Approximately 95% of hidden sites on the dark web can be classified as illegal, and with the growing number of cyber attacks happening every year, it's more important than ever to monitor the dark web for any signs of your company's information.
Using a dark web monitoring tool can be incredibly helpful in detecting any potential threats to your company's sensitive data. However, once you receive an alert from the monitoring tool, time is of the essence. It's important to act quickly and take the necessary steps to safeguard your information.
If you do discover that your company's information has been compromised and is now on the dark web, it's essential that you inform all relevant personnel, departments, and organizations. This will not only help to minimize the damage, but it will also ensure that everyone is aware of the situation and can take the necessary steps to prevent further breaches.
In today's digital age, it's more important than ever to stay vigilant and protect your company's information. By monitoring the dark web and taking swift action when necessary, you can help to ensure that your sensitive data remains safe and secure.
The objective of this initiative is to improve user safety and safeguard them against cyber hazards such as phishing, malware, and spam by monitoring the dark web.
To monitor the dark web, simply edit your monitoring profile under the section labeled "Data breaches with your information." Fitzpatrick revealed that the company currently provides security measures to Gmail users by preventing 15 billion dubious messages from reaching their inboxes each day. This amounts to roughly 9 percent of all spam, phishing, and malware attacks.
Dark web monitoring involves keeping track of any activity that takes place on the dark web, the part of the internet that is not indexed by search engines and is often used for illegal activities. It is important to be vigilant and look out for any suspicious behavior, such as unusual purchases, messages or emails sent to your customers or team. By monitoring the dark web, you can stay ahead of potential threats and protect your business from cyber attacks. Stay informed and sign up to the TechRadar Pro newsletter to receive the latest news, opinions, features and guidance for your business success.
A reliable means of tracking activities on the dark web can effectively detect most cases where your personal data is being offered for sale.
Understanding the Inner Workings of the Dark Web through Monitoring
Preventing Data Breach: Monitoring the Dark Web
Data breaches can happen to organizations without their knowledge. However, monitoring the dark web can help prevent such incidents. Though dark web monitoring tools are not illegal, they do not actively remove your information from being posted on the dark web.
After initially offering the service to Google One subscribers in March, within the next few weeks, investing in a dark web monitoring service has become more important than ever. With the increasing number of cyber threats and data breaches, monitoring the dark web for potential breaches and stolen data has become a crucial step in protecting your personal and business information. Dark web monitoring services can alert you if your information is found on the dark web, allowing you to take proactive measures to mitigate any potential damage.
When monitoring the dark web, Google provides users with a prompt warning if their information is detected. This new feature makes it simpler for users to sort through and examine their files, recognize spam, and protect themselves from potentially harmful or offensive content.
Navigating the Shadows: A Guide to Accessing the Dark Web
Tracking activities on the dark web is a complex task as it operates beyond the reach of search engines. Individuals use this platform to conceal their IP address for their safety or to carry out illegal activities without being traced. If you wish to maintain anonymity, you may choose to erase your phone number from your monitoring profile.
In order to minimize the potential dangers that come with byod policies, businesses should take into account the utilization of encryption technologies for device data and establish a clearly defined policy for the utilization of corporate resources. This encompasses the monitoring of unlawful activities such as the trade of pilfered personal information. Supporters assert that the efforts made by Google serve as an indication of the requirement for the implementation of more effective protective measures in the digitally interlinked global environment.
As an experienced copywriter, I can rewrite the given text on "Monitoring the dark web" in English. Here's my version:
If you're a Google One subscriber, you can keep tabs on whether your personal data appears on the dark web by creating a monitoring profile that includes details such as your name, address, phone number, email, and social security number.
Monitoring the dark web is a crucial task in today's digital age. The deep web, which is not indexed by search engines, is a huge part of the internet that is not accessible to the general public. The dark web, on the other hand, is a subsection of the deep web that is accessible only through specialized software. This makes it a breeding ground for illegal activities such as drug trafficking, cybercrime, and human trafficking. Therefore, it is important for businesses and individuals alike to monitor the dark web for any potential threats or risks. By doing so, they can take proactive steps to protect themselves and their assets. Don't wait until it's too late. Stay vigilant and keep an eye on the dark web.
Monitoring the dark web is a crucial aspect of cybersecurity. With the help of dark web scanning services, cybercriminal forums are constantly monitored, and any breach of sensitive information is immediately reported. This electronic ear to the ground allows for prompt identification of potential threats and helps to undermine risks. Utilizing dark web monitoring services enables companies to stay one step ahead of cybercriminals and protect their valuable data. With 24/7 monitoring, companies can rest assured that any potential threats will be identified and reported promptly, allowing for swift action to be taken to prevent further damage.
Explore further
Distributed by Smooth Adam, LLC.