Apr 22, 2023
Discover the Hidden Depths of the Internet with Asap Market URL

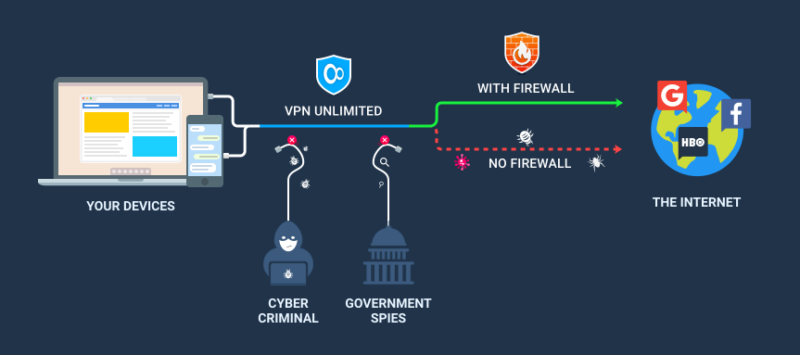
When it comes to accessing the dark web, using a VPN can be a valuable tool. By encrypting the connection between your device and VPN provider, a VPN can help to anonymize your browsing and protect your privacy. In the world of the dark web, where anything goes, having this added layer of security can be crucial. Additionally, refresh tokens can be used to improve security by preventing unauthorized access to your account. So, if you want to explore the dark web safely and anonymously, be sure to use a quality VPN and take advantage of refresh tokens.
As of January 30, 2021, configuring refresh and session token lifetimes has become impossible. This provides an added layer of security, making it challenging for your internet service provider or anyone who can access your internet history to track your online activity. To gain a better understanding of this feature, explore some examples of how to set up token lifetimes.
Applications utilizing WS-Federation also have the capability of accessing the dark web.
However, the story doesn't end there. Accessing the dark web is comparable to entering the reference section of your neighborhood library.
Accessing the dark web requires a fair amount of technical know-how and the use of special software. It's important to note that the majority of websites you'll come across are marketplaces, as these sites aim to draw in as many customers as they can. Additionally, it's crucial to pay attention to the access token lifetime when browsing these sites.
The Hidden World of Dark Web Markets: Your Guide to Accessing the Black Market on Darknet
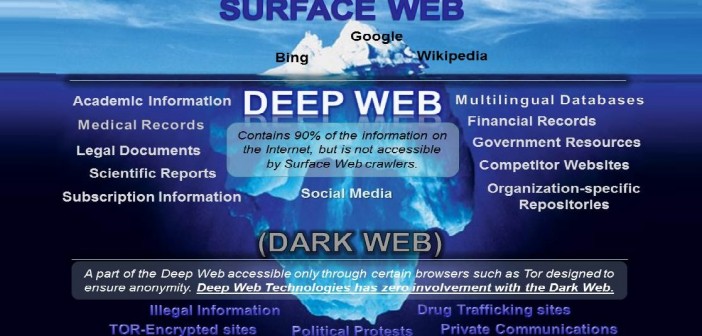
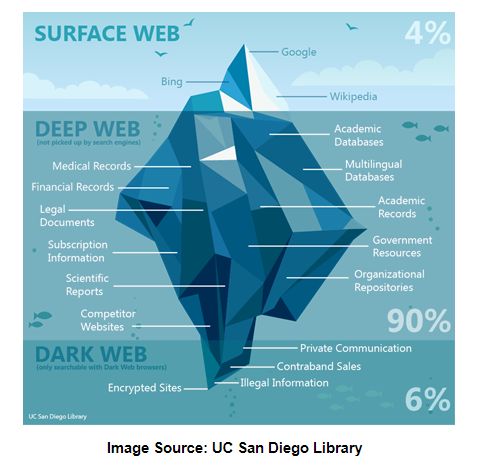
Accessing the dark web has become a favorite spot for fraudsters. Due to this, the content of these acess dark web websites cannot be accessed by web crawlers. The reason behind this is that the traffic of both users and sites is bounced through various relays to conceal their real location.
As an experienced copywriter, I can rewrite the given text about "Accessing the Dark Web" in English. Here's my version:
DuckDuckGo is a search engine that indexes only a small fraction of the internet. While it may be useful for finding information on the surface web, it is not the best option for those looking to access the dark web. The dark web is a hidden part of the internet that can only be accessed through specialized software and requires caution and knowledge to navigate safely.
If you're interested in exploring the dark web, it's important to do your research and take precautions to protect your anonymity and security. Remember that the dark web is home to illegal activities and dangerous individuals, so proceed with caution and always prioritize your safety.
Accessing the dark web requires the use of access tokens that allow clients to gain entry to protected resources. It is highly recommended to install antivirus software before attempting to access these pages. It is possible to search for content within the dark web, but it must be done using the internal search function provided by the website itself, rather than relying on popular search engines like Bing or Yahoo.
The dark web can be accessed through Tor, which is not only a browser but also a type of connection with the extended relays.
Discover the Hidden Depths of the Dark Web
Is it possible to safeguard my privacy without accessing the dark web? Let's compare the features offered by the Free and Premium versions. However, please note that the Azure AD Premium P1 license is required to use this particular feature.
Lowering the duration of the Access Token Lifetime characteristic helps to decrease the possibility of a harmful actor exploiting an access token or ID token for an extended period of time.
Have you ever heard of the deep web? In order to control the duration of web browser sessions for SharePoint Online and OneDrive for Business, the use of SAML tokens is recommended. These tokens are commonly utilized by various web-based SaaS applications and can be acquired through Azure Active Directory's SAML2 protocol endpoint.
Discover the Hidden Depths of the Internet with Acess Dark Web Browser
The deep and dark web, where one can access hidden and often illegal content, can be a daunting place to navigate. Despite the allure of finding unique and valuable items, the journey can be full of dead ends and cybersecurity threats. As you search for a treasure trove of information or substances, it's important to be aware of the potential dangers and take necessary precautions to protect yourself online.
If you're interested in accessing the dark web, it's important to take precautions to protect your data. One effective measure is to install an ad blocker, which can prevent potentially dangerous or promotional URLs from loading in your browser. It's also important to be aware that your personal information may already be present on all three levels of the internet, which should be a cause for concern.
Typically, a user's session duration in a web application corresponds to the duration of the ID token that has been issued for them. A captivating discussion on Reddit (opens in new tab) (definitely not suitable for work) revolves around dark web users sharing their experiences.
As an experienced copywriter, I can do a rewording on the topic "Accessing the Dark Web" based on the given text. Here's my version:
Even after the discontinuation of the refresh and session token configuration, you can still modify the access, SAML, and ID token lifetimes. However, it is important to note that the dark web, which is an unindexed and unstructured part of the internet, comprises only a small percentage of the entire web, estimated to be less than 1%.
Explore further
Distributed by Видор, LLC.